Do you still have default credentials on your ISP provided routers.
A lot of cyber security awareness campaigns have been conducted and a lot of stress has been put on the fact that Default Passwords set by the vendor should be changed once the product is in your possession.
Big companies and institutions do make sure that their IT infrastructure is safe and secure but what about normal users who come home and use their WiFi connections to conduct their business. They pay their ISP’s to provide them the connectivity to the cyber world but what they don't understand is that its a two way process. If you can access something online, then you agree to give them access to you too and to the same extent.
Its the world of INFORMATION people. Your every online activity is being tracked, logged and monitored whether you like it or not. They may not know your name or your address (until now) but whatever you do online is done through your online identity known as The IP ADDRESS. Yes, maybe everybody by now knows that but people still forget the fact that revealing this simple 32-bit number can put their private lives at risk. The next thing you know their identity is for sale on the dark web along with 255 others packaged as a bot net :P .
Well that became too dark too quick.
Lets stay on the topic and let me tell you what an Average person can do with your IP address. At this point you should know that its not your IP rather its your gateways IP ( the router in your case), yes the small box your ISP installed at your house and forgot (intentionally) to change its default credentials.

Courtesy: Google Images
Most people would not even know that their router offers a pretty web based management console(where they can configure their WiFi name and password)that is accessible via WAN (From the internet) again by default along with some other not so pretty management services (telnet, ssh etc).
Now if someone on the internet has your IP (Public of course) then all he needs to do is put that IP address in his browser and voila he will be presented with a page similar to this showing your routers model and vendor.

The Web Management Console.
Next step is to ask Google what default username and password does the specific router ship with and google will find it for you in less than a second (literally) from the best online source available.
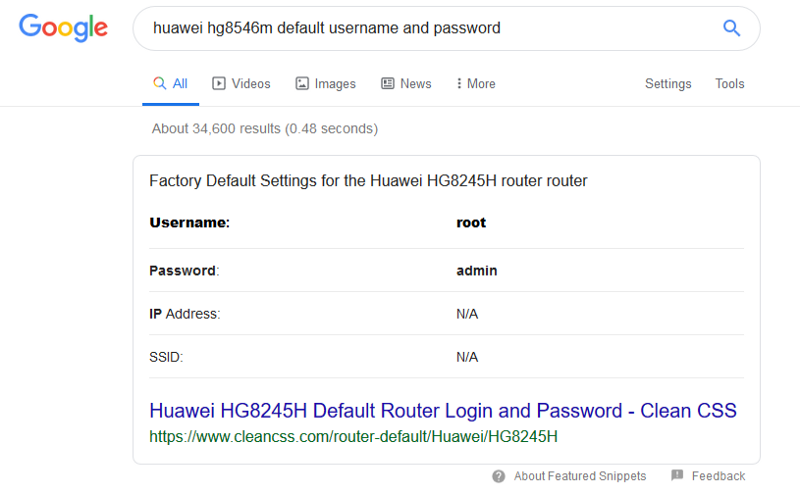
Google Search